Como todos sabemos,Elon Muské um homem ocupado. Ele administra seis empresas, incluindoTesla, Assim,Twitter, eSpaceX. Apesar de sua programação lotada, Musk tem energia sem limites. Ele também consegue twittar dez a dezenas de tweets todos os dias.
Após a eleição presidencial, Musk se tornou uma figura proeminente aos olhos do público. Mas entre todos os seus deveres, ele lidera oDOGEDepartamento de Eficiência.
O que muitos podem não esperar é que Musk encontre tempo para jogar videogames. De fato, ele afirma ser um jogador profissional de classe mundial. Isso é pelo menos o que ele diz.
Reivindicações de jogos de Musk
Em novembro do ano passado, Musk apareceu emJoe RoganS.podcast. Ele alegou ter atingido o top 20 emDiabo IVmundialmente.
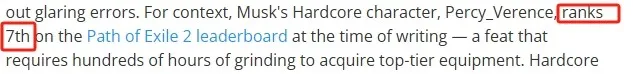
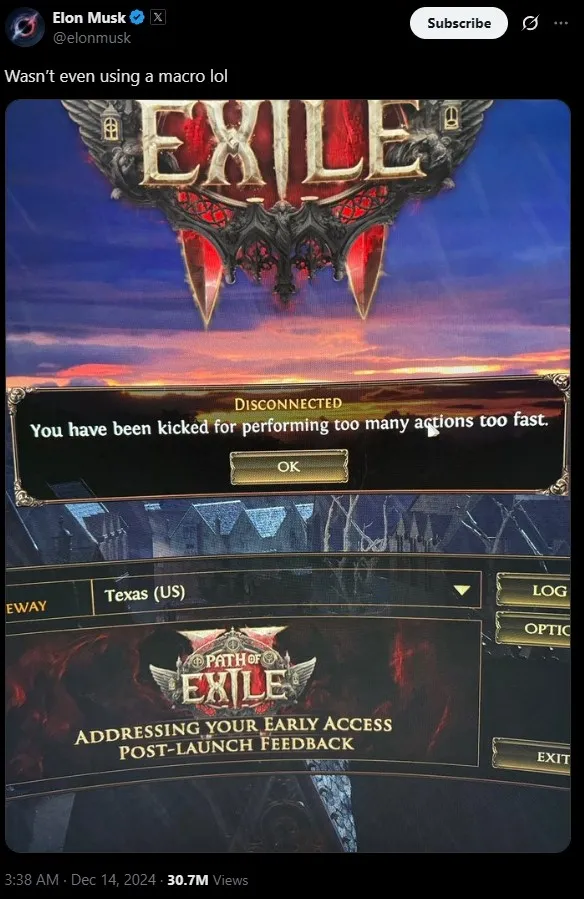
Mais tarde, em dezembro, um jogo semelhante chamadoCaminho do exílio 2foi lançado. Musk, o auto-proclamado jogador “Top 20”, alcançou as melhores fileiras emCaminho do exílio 2dentro de apenas um mês.
Em janeiro, os relatórios confirmaram que o personagem de Musk havia alcançado o 7º lugarCaminho do exílio 2A tabela de classificação oficial do jogo, apenas um mês após o lançamento do jogo.
Seu personagem era extremamente alto e seu equipamento era excelente. Isso significava que ele passou centenas de horas movendo o jogo, coletando itens. É provável que ele jogasse por mais de oito horas por dia, em média.
A verdade por trás dos rankings
Mas muitos começaram a se perguntar como Musk, que está ocupado administrando várias empresas, pode ser tão bom em dois jogos. Não demorou muito para os detetives da Internet começarem a cavar. Eles descobriram que suas duas contas de “classe mundial” provavelmente foram infladas.
Primeiro,Diabo IVNa verdade, não possui um sistema oficial de classificação. A alegação de Musk de estar no “Top 20 do mundo” veio de uma tabela de classificação de terceiros. Para ser franco, essa tabela de classificação era obscura. Havia menos de 1.000 participantes, enquantoDiabo IVtinha pelo menos centenas de milhares de jogadores. A maioria da mídia de jogos apontou que Musk era hábil em jogar, mas alegando estar no top 20 era um exagero.
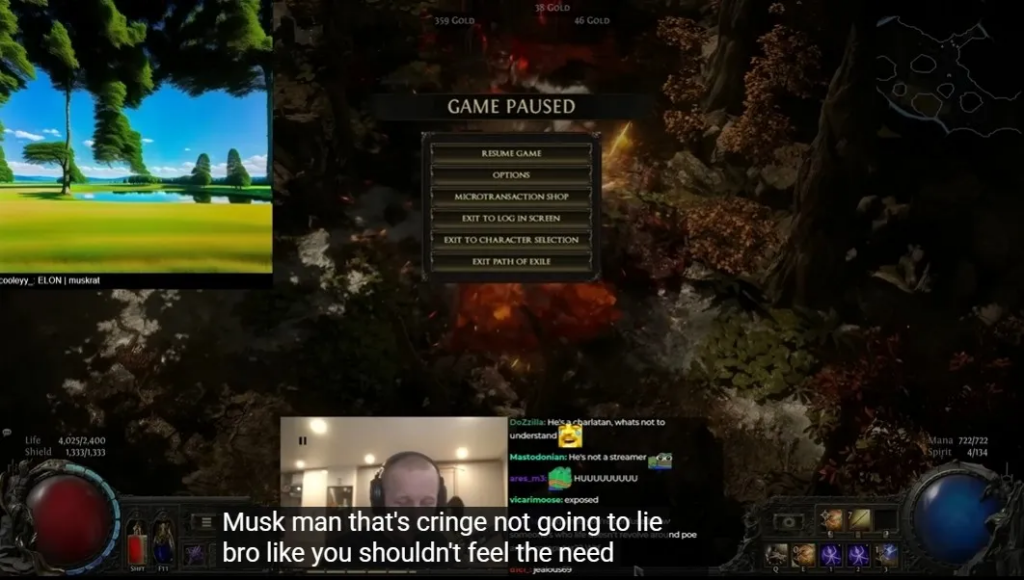
Quanto ao novoCaminho do exílio 2, Musk não parecia tocar em alto nível. No início de janeiro, Musk transmitiu mais de uma hora deCaminho do exílio 2. Suas verdadeiras habilidades foram expostas.ForbesA revista destacou os erros de estreia: os itens inúteis da Musk acumulados em seu inventário e não os descartaram. Quando itens valiosos apareceram, ele não os pegou. Musk também esqueceu de beber poções quando seu personagem ficou sem mana durante uma luta contra chefes.
Uma serpentina profissional, comentando sua jogabilidade, disse: “Musk, honestamente, você está me envergonhando. Você não deveria estar mentindo sobre isso”.
Drama ao vivo de Musk
Em janeiro, Musk foi visto emTrump’sinauguração. Enquanto isso,Caminho do exílio 2Os jogadores notaram que sua conta estava silenciosamente logada.
Claramente, a alegação de Musk de ser um jogador de “classe mundial” provavelmente foi o resultado da contratação de jogadores profissionais.
De acordo com umRedditAnálise do usuário, é altamente provável que Musk tenha usado um reforço chinês. Mais tarde, Musk admitiu contratar um reforço, mas não achou vergonhoso. Ele explicou que alcançar os principais rankings emDiabloeCaminho do exílioExigiu um esforço de equipe, portanto, a contratação de ajuda não era incomum.
A última sessão de jogo
Após a controvérsia, Musk ficou baixo no mundo dos jogos. No entanto, recentemente, ele retomou os jogos. Em 5 de abril, Musk Livestregou quase duas horas deCaminho do exílio 2a bordo de seu jato particular, enquanto testavaStarlinkS está a bordo Wi-Fi.
Em toda a transmissão ao vivo, sua jogabilidade estava longe de ser impressionante – ele até morreu para o chefe do tutorial.

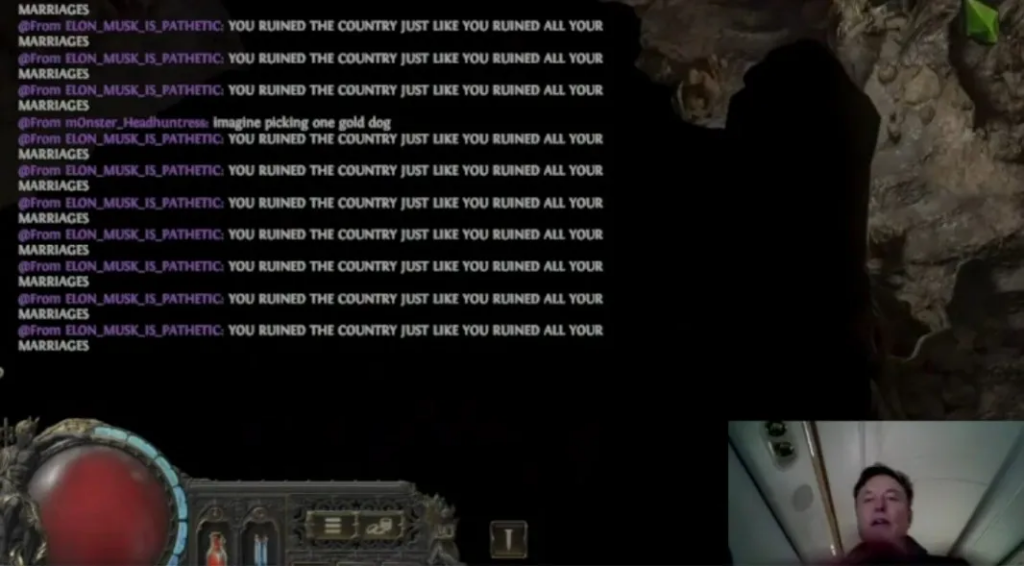
Mas a pior parte do fluxo não foi a jogabilidade. Musk foi bombardeado com mensagens privadas abusivas ao longo da sessão. Ele permaneceu estoico, bloqueando algumas mensagens, mas dizendo pouco. Nos primeiros 10 minutos, Musk recebeu inúmeras mensagens de ódio. Um usuário havia criado uma conta chamada “Elon_is_a_pedophile” e enviou um spam para o bate -papo: “Você não tem amigos de verdade, você morrerá sozinho!” Variações múltiplas desta mensagem se seguiram.
Havia mais mensagens como: “Musk é patético” e “você arruinou este país, assim como arruinou todos os seus casamentos!”
Uma mensagem até alegou ser da suposta mãe de Musk, “Ashley St. Clair”, exigindo pensão alimentícia.
Musk parecia imperturbável, mas acabou bloqueando o usuário.
Reflexões sobre o fluxo
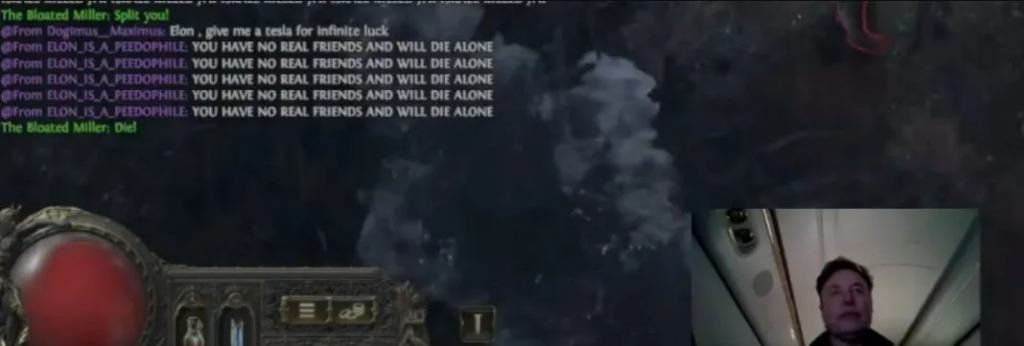
EmboraCaminho do exílio 2Tem a opção de bloquear mensagens privadas, Musk optou por não usá -lo. Alguns espectadores até tentaram ajudá -lo a bloquear as mensagens ofensivas, mas Musk deixou o ódio inundar. Parecia que ele havia crescido imune a esse abuso.
No final do riacho, o jogo de Musk congelou, e ele disse casualmente: “Bem, estou desconectado”. Seu personagem morreu logo depois, e ele terminou abruptamente a transmissão ao vivo, posteriormente excluindo o vídeo do Twitter.
Curiosamente, mesmo após o término do fluxo, as mensagens de ódio continuaram a inundar sua caixa de bate -papo.
Conclusão
A transmissão ao vivo de Musk, suas reivindicações de jogos de “classe mundial” e os abusos on-line que se seguiram adicionaram outra camada à sua persona pública. Ele está constantemente sob um microscópio, uma mistura de admiração e crítica, com muito pouco espaço para ele ser “humano”.

Independentemente de suas habilidades de jogo serem genuínas ou terceirizadas, parece que a Internet continuará examinando Musk – tanto por seus sucessos quanto suas falhas. Somente o tempo dirá se Musk continuará sendo transmitido ou deixará suas habilidades de jogo desaparecer no fundo de seus muitos empreendimentos.