iPhone 的新时代
苹果可能很快就会加入可折叠手机的竞赛。
分析师杰夫·P声称苹果即将推出iPhone 至尊版将有一个钛铝混合框架。
他给投资者的报告表明,iPhone折叠和iPhone空气,预计在2026年,将使用这种新的金属组合。
这标志着苹果向更轻、更强、更优质的设计迈出了大胆的一步。
不同的分析师,不同的金属
今年早些时候,Ming-Chi Kuo做出了类似的预测。
然而,两位分析师对苹果的具体材料选择存在分歧。
Pu相信苹果会混合钛和铝。
郭预计钛和不锈钢。
他还认为合页将结合两者钛和液态金属,提高力量和灵活性。
这样的设计选择可以让苹果的可折叠设备在耐用性和便携性之间达到无与伦比的平衡。

超薄、超坚韧
泄密表明苹果的可折叠 iPhone 可能只测量4.5毫米打开时——比传闻中的更薄iPhone空气。
为了实现这一目标,苹果需要像钛这样坚韧的材料。
这iPhone 15 专业版已经证明了钛的弹性,能够经受住剧烈的弯曲测试。
通过扩大钛的使用,苹果增强了其设备的性能,同时保持了它们的时尚。
未来的模型如iPhone 18 折叠和iPhone 18空气可能会遵循这条道路,采用相同的混合金属方法。
为什么钛铝是明智之举
钛合金通常含有微量的铝。
苹果可能会通过战略性地混合这两种金属来进一步推动这一想法。
钛虽然较重,但却为关键部件提供了强有力的支撑。
铝有助于平衡重量。
它们共同打造出轻巧而坚固的结构,非常适合可折叠手机。
名字游戏:为什么“Ultra”有效
报告来自朝九晚五建议苹果可能会跳过“折叠”并继续使用iPhone 至尊版反而。
这个名字符合苹果的分层品牌逻辑。
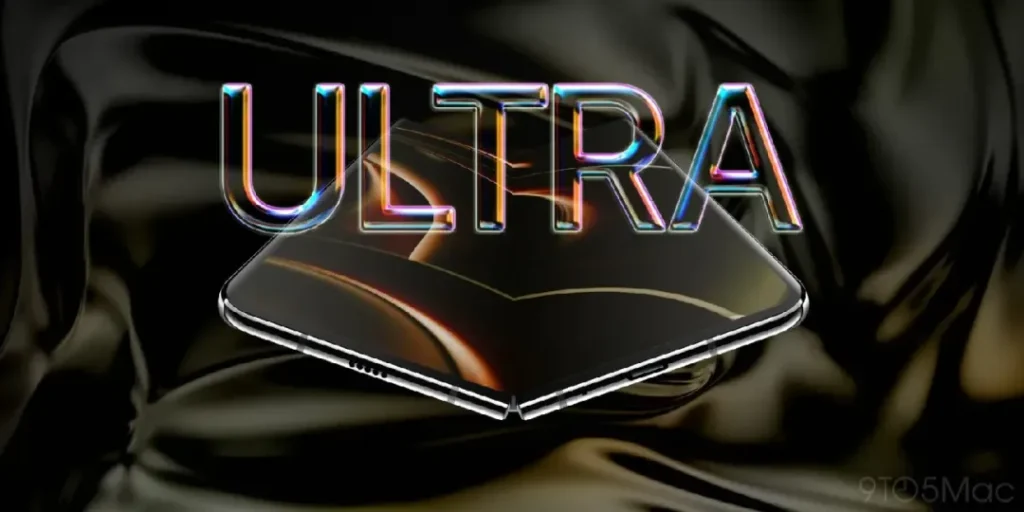
就像M3超芯片超越M3 Max,“Ultra”意味着超越专业最大。
它标志着排他性和尖端性能。
还有一个营销角度。
这苹果手表Ultra,售价为799 美元,成本几乎是标准系列型号的两倍。
分析师认为可折叠 iPhone 可能突破2000美元大关,几乎翻倍iPhone 17 Pro 最大价格。
“Ultra”听起来高端且令人向往,而“Fold”可能会让人们想起脆弱的实验手机。
这就是为什么苹果的选择更多是心理上的而不是技术上的——它推销的是雄心,而不仅仅是创新。
与此同时,iPhone 17 也大放异彩
这苹果17已经推出了多项可靠的升级。
它具有一个6.3英寸屏幕,120Hz刷新率, 和256GB 基本存储。
这些改进使其成为苹果迄今为止最全面的型号之一,并且很可能成为今年的主要畅销产品。
最后的想法
如果泄密属实的话iPhone 至尊版可能会重新定义高端智能手机的含义。
它承诺钛铝混合框架, 一个薄而耐用的构造,和一个价格与其名称相符。
苹果此举显示了突破设计、技术和奢华界限的信心。
iPhone 的可折叠未来可能指日可待——而且它在各个方面都看起来非常超棒。